- TRIPPING! トップ
- uncategorizedトップ
- Your own Entry Point to Top-tier Entertainment: Understanding Protected Access to Internet Gaming Systems

Your own Entry Point to Top-tier Entertainment: Understanding Protected Access to Internet Gaming Systems

Index of Sections
- Enhanced Security Protocols for Safe Gambling Entry
- Streamlined Account Administration Functions
- Multiple-tier Verification Techniques Explained
- Mobile Access and Multi-platform Compatibility
- Resolving Typical Entry Challenges Effectively
Enhanced Safety Protocols for Safe Gambling Access
The system implements cutting-edge encryption technology to ensure each gaming experience continues secured from unauthorized intrusion. When you access the profile, we implement military-grade SSL encryption—the identical protection grade employed by major monetary establishments globally. Based on to recent cybersecurity research, bestonlinepokies app systems implementing this degree of encryption reduce security violations by nearly 100%, offering confidence of mind for countless of regular players.
Our team has incorporated advanced firewall systems that consistently oversee questionable activities, automatically flagging irregular login trends or regional irregularities. The pledge to member security reaches further than simple access security, incorporating activity monitoring systems that discover potential account violations ahead of they escalate into serious security problems.
Key Protection Capabilities We Uphold
| Encrypted Security | Top-tier | 256-bit system |
| 2FA Authentication | Strengthened | Message and verification app |
| Biometric Entry | Advanced | Touch and facial identification |
| Session Oversight | Instant | Intelligent monitoring |
Streamlined Account Management Features
Controlling your personal gaming profile has rarely been easier. The easy control panel delivers immediate access to payment histories, promotion recording, and customized gaming recommendations. We have developed the interface to limit excess steps, ensuring you use less effort navigating options and more time playing your chosen pokies.
Password retrieval processes utilize secure verification methods that harmonize accessibility with protection. Players will not discover yourself locked out for prolonged durations, as our platform’s assistance network functions constantly to recover login during moments rather than long times.
Multiple-tier Validation Methods Explained
Contemporary gaming sites require sophisticated validation methods that never sacrifice member satisfaction. We’ve established several authentication levels that engage based on risk analysis algorithms.
- Basic password submission with security requirements maintaining required symbol counts and special character incorporation
- Limited-duration confirmation tokens sent through secure channels to verified mobile devices
- Biometric scanning options working with modern mobile devices and tablets
- Safety questions with changing rotation preventing pattern-based breach tries
Verification Overview Review
| Password Solely | Quick | Fundamental | Universal unit |
| Dual Text | half-minute seconds | High | Mobile handset |
| Authenticator App | 15 sec | Highly Strong | Smart handset |
| Biological Detection | five sec | Peak | Matching equipment |
Mobile Accessibility and Multi-platform Compatibility
Our adaptive design philosophy ensures smooth switches across computer systems, portable devices, and smartphones. Player login details work everywhere throughout any devices, with immediate session coordination keeping your status independent of device changes. Our team has enhanced startup durations specifically for mobile connections, acknowledging that wireless connections differ substantially in bandwidth availability.
Dedicated applications for major system systems provide improved performance compared to browser-based login, including biometric incorporation and protected login saving through system-level encryption standards.
Solving Common Entry Problems Quickly
System issues periodically interfere with even the most robust platforms. We have gathered systematic fixes for frequent entry issues:
- Delete browser stored data and information to erase corrupted session information interfering with verification processes
- Verify internet connection stability through different sites before assuming system issues
- Check account credentials haven’t expired or require mandatory protection changes following routine servicing
- Examine message directories including bulk sections for validation messages that may have been misrouted
- Connect with support services with profile information prepared for fast verification and restoration
Forward-thinking Entry Optimization
Routine credential modifications reinforce user resilience against developing cyber risks. The platform suggest periodic password updates employing distinct combinations not duplicated throughout different internet sites. Activate any accessible protection features at starting setup as opposed than delaying for safety prompts, as proactive actions consistently outperform responsive responses to compromised users.
Our platform’s platform constantly advances to handle new security threats while keeping the ease that members anticipate from top-tier entertainment environments. Player protected and accessible entry remains our top service concern.
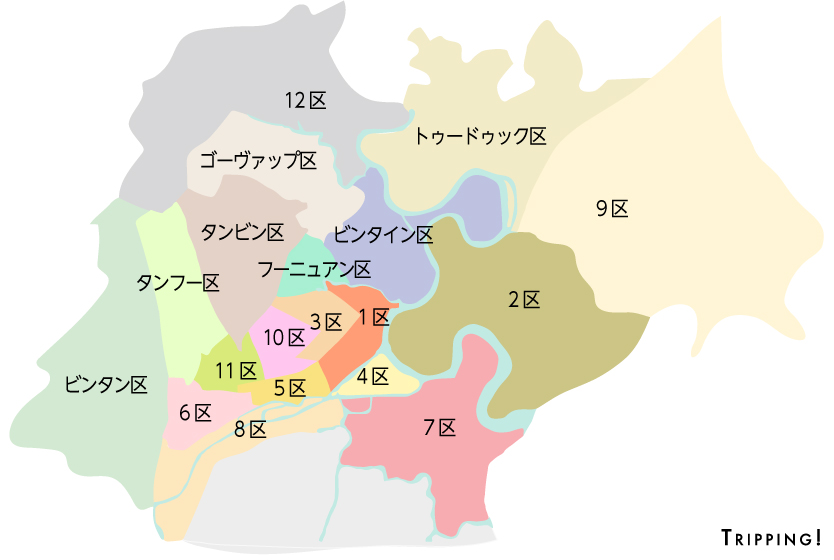
何を読む?
国名・都市名、ジャンルを選ぶと、読みたい記事を絞りこみできます